If you operate critical infrastructure, “ICS and SCADA” is not just terminology. It defines how process control is engineered, where safety and availability constraints dominate, and how cyber risk moves across Purdue zones, remote access paths, and vendor-maintained interfaces. Most security guidance stops at definitions and control lists. That helps, but it does not answer the question practitioners carry during audits, tabletop exercises, and incident response: which attack paths are actually possible in our environment, and how can we validate them without putting production at risk?
This article breaks down how ICS and SCADA systems are typically built, common failure modes that turn “secure-by-design” assumptions into exposure, and a practical validation approach that fits operational constraints. For deeper background on safe validation using simulation, see How Digital Twins Enable Safe, Comprehensive OT Security Testing. If you are aligning findings to governance and compliance outcomes, OT Risk Assessment provides a useful structure.
Concise definitions: ICS vs SCADA vs OT
ICS (Industrial Control Systems) is the umbrella term for systems that monitor and control industrial processes. It includes PLC-based control, DCS, SIS, and SCADA. SCADA (Supervisory Control and Data Acquisition) is a class of ICS focused on supervisory monitoring and control across distributed assets, typically with a central control room and remote sites. OT (Operational Technology) describes the broader environment that runs physical processes, including the people, procedures, networks, endpoints, and engineering workflows that support ICS.
Why the distinction matters for security:
- ICS security decisions are constrained by safety, determinism, and uptime.
- SCADA deployments often increase the attack surface through distributed telemetry, radio or cellular links, and remote operations.
- OT security covers more than the control network. Engineering laptops, historian systems, vendor remote access, and identity boundaries often determine real exposure.
A practical takeaway: when someone says “secure the SCADA,” ask which components they mean (HMI, historian, field RTUs/PLCs, comms gateways, engineering workstation, domain services) and what operational constraints apply (change windows, safety cases, vendor support boundaries).
How ICS and SCADA systems are typically architected
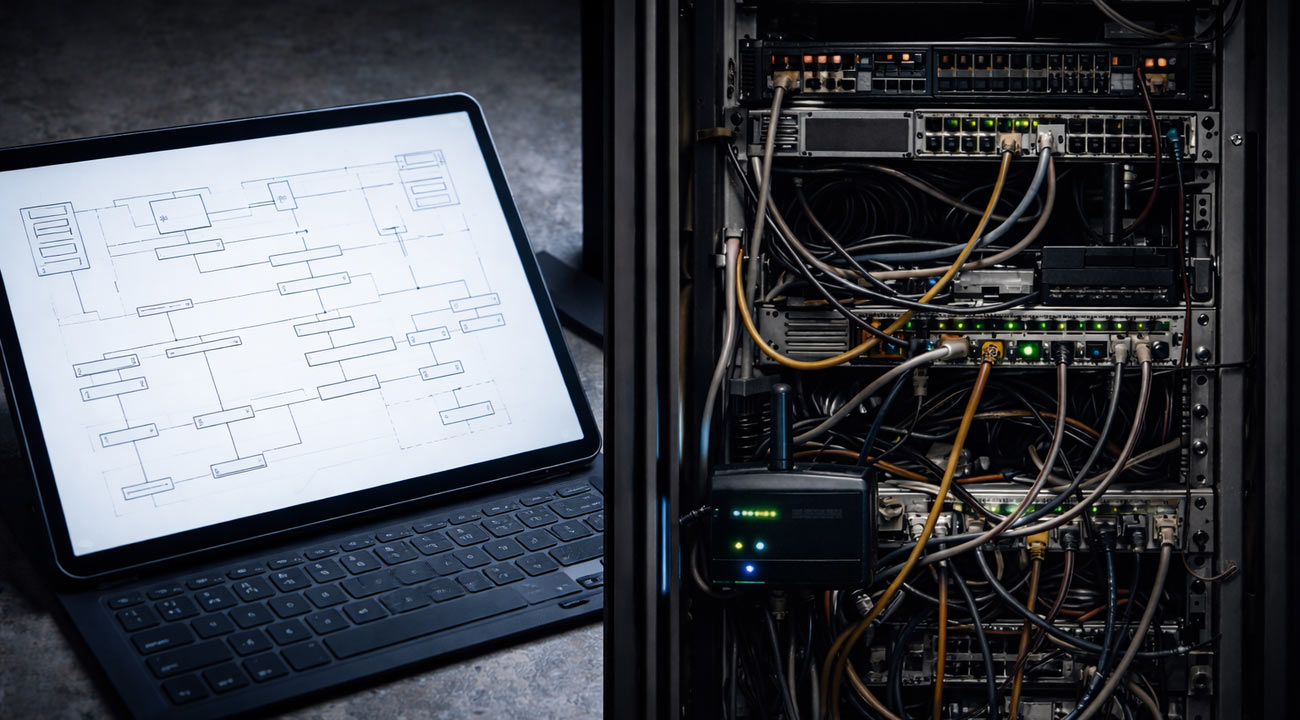
While architectures vary, most critical infrastructure control systems have recurring building blocks:
- Field layer
- PLCs, RTUs, IEDs, drives, actuators, sensors
- Often long-lived, sometimes running legacy firmware
- Common constraints: limited CPU and memory, limited cryptography, operational sensitivity to scanning
- Control and supervisory layer
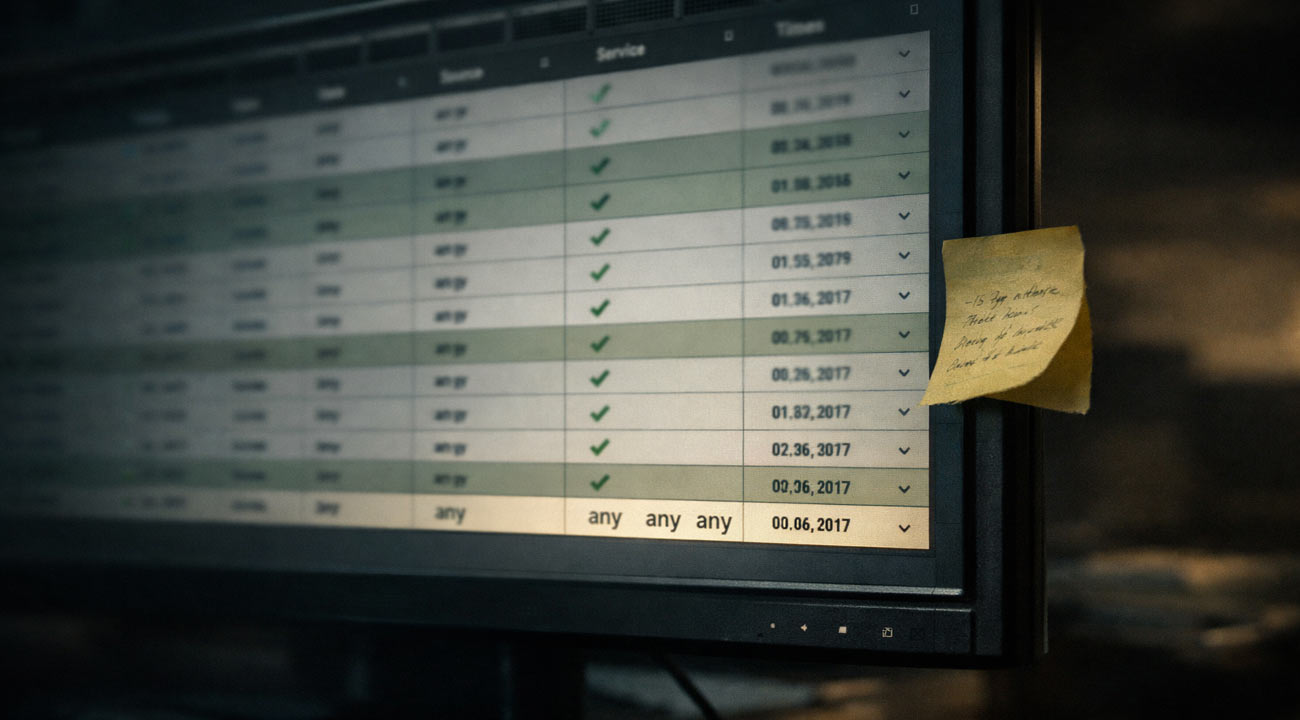
- HMIs, SCADA servers, data concentrators, alarm servers
- OT protocols (often cleartext) between HMIs and controllers
- Redundancy is common, but security segmentation is inconsistent
- Engineering and maintenance workflows
- Engineering workstations used for logic changes and firmware operations
- Portable media and vendor software are frequent ingress points
- “Temporary” connectivity often becomes permanent
- Operations and business integration
- Historians, reporting, MES, batch systems
- IT-OT connectivity for analytics, compliance, and performance
- Identity boundaries and remote access solutions that bridge zones
- Remote sites and communications
- Power grid SCADA systems and oil and gas SCADA networks may span wide geographies
- Water treatment SCADA systems may have remote pump stations and telemetry networks
- Links can include leased lines, MPLS, microwave, cellular, satellite, serial, and radio
Where risk concentrates is not only in controllers. It is frequently in the intersections: the remote access path that bypasses segmentation, the engineering laptop that touches multiple cells, or the historian connector that provides a convenient bridge between IT and OT.
If you need a broad OT security grounding before diving into validation, Complete Guide to OT Security: Protecting can help align terminology with control objectives.
Threat model: common attack paths against critical infrastructure control systems
Attackers rarely start in the control network. Most real intrusions progress along a chain of access and privileges, then pivot into ICS and SCADA environments.
Common attack paths include:
- Remote access to OT
- Vendor VPNs, jump servers, remote desktop gateways, modem or cellular management interfaces
- Weak MFA enforcement, shared accounts, and unmanaged endpoints
- IT to OT pivots
- Flat routing, permissive firewall rules, shared identity services, dual-homed hosts
- Historian and reporting interfaces that accept inbound connections from IT
- Engineering workstation compromise
- Phishing, browser exploitation, supply chain issues in vendor tooling
- Credential reuse from IT, local admin sprawl, weak application control
- Protocol and trust abuse inside OT
- Cleartext protocols, unauthenticated control messages, permissive “write” operations
- Misuse of legitimate tools: remote programming, logic downloads, tag writes
- Third-party and temporary connectivity
- Contractor laptops, support tunnels, “short-term” rules kept for convenience
- Assets outside CMDB, unmanaged switches, ad hoc wireless bridges
This is why control checklists often miss material risk. A site can have segmentation on paper, yet one support pathway creates an effective single zone.
If you are evaluating how modern adversaries focus on stealthy access and long dwell time, Can Your OT Defenses Stop Volt frames the problem in operational terms without assuming you can run disruptive testing in production.
What makes ICS and SCADA security different from traditional IT security
ICS and SCADA environments are not “just IT with older devices.” Differences that matter for security validation:
- Availability and safety dominate
- Production disruption can trigger safety events, regulatory reporting, environmental impact, and equipment damage
- Many plants treat certain change activities as safety-relevant and require formal review
- Deterministic communications and fragile endpoints
- Controllers and comms gateways can react poorly to aggressive scanning
- Latency and packet loss can have process consequences
- Long lifecycles and vendor constraints
- Patch cadence may be annual or less frequent
- Vendor support contracts may restrict changes or endpoint tooling
- Trust assumptions inside the control network
- Many protocols assume a trusted network, not adversarial presence
- Monitoring is valuable, but alone it does not prove whether a path is exploitable
- Evidence requirements are different
- OT leadership often needs proof that aligns to operational constraints: which assets could be impacted, under what conditions, and how to reduce risk without breaking the process
These constraints make “run a pentest” an incomplete answer. A traditional pentest can be useful, but it is often time-boxed, narrow in scope, and limited by safe engagement rules that prevent realistic validation of control impacts.
Why many ICS and SCADA programs struggle to prove risk reduction
Mature teams often have inventories, vulnerability feeds, and network monitoring, yet still struggle to answer:
- Which vulnerabilities are reachable from a likely entry point?
- Which credentials and trust relationships turn a low-severity weakness into a high-impact path?
- Which controls actually interrupt the path rather than shifting it?
Common reasons:
- Vulnerability data is not contextual
CVEs and advisories are necessary, but without reachability and privilege context, remediation becomes a backlog rather than a risk reduction plan. - Architecture documentation is incomplete
Critical infrastructure control systems evolve. Mergers, expansions, OEM upgrades, and emergency fixes create drift between diagrams and reality. - Validation is constrained by fear of disruption
Teams avoid testing because they cannot risk plant instability. As a result, they rely on assumptions. - Point tools do not connect exposure to outcomes
Monitoring can show what happened. It does not always show what could happen, and under which controls.
The gap is not effort or intent. It is the lack of a safe, realistic way to validate attack paths end-to-end.
A practical framework: safe validation of ICS and SCADA risk using digital twins and attack-path analysis
To validate real-world industrial cyber risk without putting production at risk, use a validation workflow designed for OT constraints. The core idea is to model the environment, test plausible attacker behavior safely, and produce outputs that directly drive engineering decisions.
Step 1: Define the outcomes and constraints
- Outcomes: prevent loss of view, loss of control, unsafe state, or prolonged downtime.
- Constraints: no unapproved changes to control logic, no packet floods, no intrusive scanning on sensitive segments, strict maintenance windows.
- Scope: which plants, which cells, which remote sites, which vendor paths.
Step 2: Gather the minimum viable data set
You do not need perfection to start. Useful inputs typically include:
- Network segmentation and routing data (firewall rules, VLANs, ACLs).
- Asset identity (key servers, HMIs, engineering stations, historians, remote access gateways).
- Authentication and trust (AD domains, local accounts, shared credentials, service accounts).
- Remote access patterns (vendor support workflows, jump hosts).
- Known vulnerabilities and configuration weaknesses (from scanners where safe, or passive sources).
Objection: “Are we mature enough to create a digital twin?
A digital twin for security validation does not need full process physics. It needs enough fidelity to represent reachable paths, identity boundaries, and control points. Many teams begin with partial data and improve iteratively.
Step 3: Build a safe environment for testing
This is where digital twins and simulation are valuable. Instead of probing production, replicate relevant elements or simulate interactions to validate assumptions. For a deeper explanation of how digital twins support safe testing, see How Digital Twins Enable Safe, Comprehensive.
Step 4: Model attacker objectives and paths
Focus on realistic paths:
- Initial access: remote access, contractor endpoint, IT compromise.
- Privilege escalation and credential harvesting.
- Lateral movement: from IT services to OT services, from site to site.
- OT impact path: from an HMI or engineering tool to a controller write action.
Produce attack-path outputs that answer:
- Preconditions (which credentials, which reachable services).
- Choke points (where segmentation, MFA, or application control interrupts the path).
- Blast radius (which assets and process areas are exposed).
Step 5: Validate safely, then prioritize fixes by path reduction
Instead of prioritizing by CVSS alone, prioritize by how much each fix collapses reachable paths to high-impact assets.
Examples:
- Tighten firewall rules between historian and OT cells to remove a pivot, not just reduce noise.
- Replace shared vendor accounts with named accounts and MFA on the actual jump host used.
- Apply application allowlisting on engineering workstations to reduce tool abuse.
- Add secure remote access controls that enforce device posture before OT connectivity.
Step 6: Re-validate continuously
Industrial environments change. New remote sites come online, firewall rules are added for troubleshooting, and vendors update software. Continuous validation confirms whether changes reintroduced paths.
For a practitioner view of non-disruptive testing approaches in OT, Effective and Non-Disruptive OT Security Testing expands on how to reduce operational risk while still producing meaningful findings.
What you get at the end: outputs that engineering and leadership can act on
A useful ICS and SCADA security validation deliverable should not be a generic report. It should translate risk into decisions.
Expect outputs such as:
- A ranked list of attack paths to high-risk assets (for example, paths to engineering workstations, domain controllers serving OT, key SCADA servers, safety-relevant control points).
- Evidence of which controls stop which steps in the path.
- Remediation recommendations tied to operational constraints (what can be changed in a maintenance window, what needs vendor involvement, what requires a procedure change).
- A re-test plan that confirms risk reduction without disruptive production testing.
If you are aligning these outputs to governance, audit, or regulatory expectations, grounding the work in an OT-focused assessment structure helps. OT Risk Assessment provides a practical way to connect technical findings to risk treatment and ownership.
FAQs
Is SCADA the same thing as ICS?
SCADA is a type of ICS. ICS is the umbrella term for industrial control technologies, including SCADA, DCS, PLC-based control systems, and safety systems. SCADA typically emphasizes supervisory control across distributed assets, while ICS covers both supervisory and local control architectures.
Will validating ICS and SCADA security disrupt production?
It does not have to. A safe validation approach uses operational guardrails, relies on passive data sources where possible, and validates attacker paths in a simulated or digital twin environment instead of probing production devices. When any production interaction is required, it should be tightly scoped, approved, and coordinated with operations.
Is this better than a traditional OT pentest?
It addresses a different problem. Traditional pentests can identify weaknesses, but they are often constrained from testing realistic OT-impact scenarios in production. Attack-path validation using simulation focuses on whether high-impact paths are feasible end-to-end and what specific control changes break those paths, with minimal operational risk.
Do we need perfect asset inventory and network diagrams to start?
No. You can start with a minimum viable data set such as segmentation rules, key asset roles (SCADA servers, HMIs, engineering workstations, historians, remote access), identity boundaries, and known vulnerabilities. The model can be refined as data quality improves, and re-validation helps keep it current as the environment changes.
What deliverables should an ICS and SCADA security assessment produce?
Look for ranked attack paths to high-risk assets, evidence for which controls stop which steps, remediation actions tied to operational constraints, and a re-test plan that confirms risk reduction. The most useful output connects technical findings to decisions that OT engineering and leadership can execute.
Call to Action
If you need to move beyond definitions and prove which ICS and SCADA attack paths are realistic in your environment, Frenos can help you validate OT security safely using digital twin based simulation and attack-path analysis. Request an OT Security Assessment to get actionable findings that map to operational constraints and compliance needs.



.jpg)
