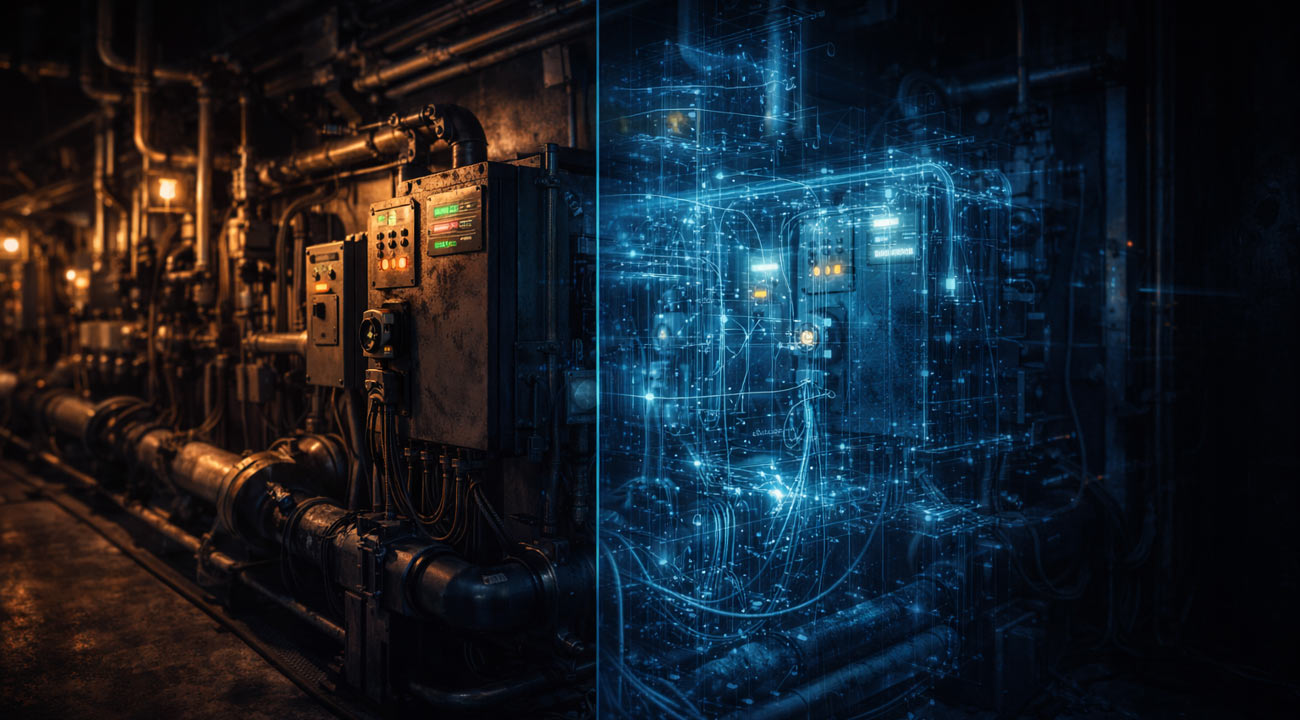
SCADA environments are built to keep physical processes stable, not to make security testing convenient. That mismatch is why “SCADA cyber security” is less about deploying a single tool and more about understanding how your control system actually behaves, where the real trust boundaries are, and how to validate defenses without putting operations at risk.
This article explains how SCADA systems work, why they are uniquely hard to secure, and a practical framework you can use to reduce risk in critical infrastructure and industrial environments. It also addresses a persistent pain point: many of the most valuable security tests are the hardest to run in production. Frenos approaches that problem with safe, full-scope validation using a digital twin of the industrial environment, so teams can simulate realistic attack paths and measure control effectiveness without touching production systems. If digital twin based testing is new to you, start with How Digital Twins Enable Safe, Comprehensive OT Security Testing or the deeper primer Digital Twins in OT Cybersecurity.
What is SCADA cyber security (definition and scope)
SCADA cyber security is the set of technical controls, operational processes, and validation activities used to protect supervisory control and data acquisition systems from cyber threats that could impact safety, reliability, product quality, or service continuity.
In practice, SCADA cyber security spans:
- Visibility and asset inventory across SCADA servers, HMIs, historians, engineering workstations, PLCs/RTUs/IEDs, and network infrastructure
- Secure architecture (zones, conduits, remote access, identity)
- Detection and response tuned for OT constraints
- Vulnerability management and change control that respects uptime and safety requirements
- Validation through SCADA vulnerability assessment and SCADA penetration testing methods that do not destabilize the process
Unlike typical IT security programs, SCADA security must account for deterministic control traffic, long-lived devices, vendor and integrator dependencies, and tightly coupled operational procedures.
How SCADA systems work: the control loop, communications, and trust assumptions
To secure SCADA, it helps to map the functional layers and how decisions flow.
- Field layer (sensors and actuators)
Sensors measure state (pressure, flow, voltage, temperature). Actuators change state (valves, breakers, motors). These endpoints are often controlled indirectly by PLCs, RTUs, or IEDs.
- Control layer (PLCs, RTUs, IEDs)
Controllers execute logic, often with strict timing constraints. Many are engineered for availability and determinism, with limited native security controls, limited logging, and constrained patching windows.
- Supervisory layer (SCADA servers, HMIs, historians)
Operators observe process state via HMI, acknowledge alarms, and issue supervisory commands. Data is stored in historians for reporting, QA, and troubleshooting.
- Engineering and maintenance workflows
Engineering workstations and vendor tools are used to configure logic, firmware, setpoints, and communications. These workflows often carry the highest privilege and the highest risk.
- Communications and protocols
SCADA networks frequently rely on industrial protocols that were designed for reliability rather than authentication and encryption. Even when secure variants exist, mixed estates and legacy links are common.
Where security gets hard is in the implicit trust model: many devices trust anything on the control network, many workflows assume a small set of “known” stations, and operational urgency can override change control. Attackers exploit this by moving laterally to the engineering plane, abusing remote access, or manipulating supervisory functions to change process outcomes.
Why SCADA is hard to secure: constraints that change the playbook
SCADA security programs often struggle for reasons that are structural, not due to lack of effort.
Availability and safety are first order requirements
A scan, a misconfigured IDS, or a poorly timed patch can trigger latency, device faults, or nuisance alarms. That makes teams cautious about testing and change.
Legacy and heterogeneity
You may have decades of equipment, multiple vendors, and custom integrations. Some components cannot be patched, or patching is bound to outages, regulatory approvals, or OEM support windows.
High impact of credential and engineering compromise
In many environments, compromising an engineering workstation or vendor remote access path provides the ability to alter PLC logic, firmware, or setpoints. That is fundamentally different from typical IT lateral movement.
Thin telemetry and limited authentication
Some endpoints provide minimal logs. Some protocols have limited security primitives. This pushes defenders toward network based monitoring and strict architecture.
Operational ownership is distributed
SCADA cyber security is shared across operations, engineering, IT, vendors, and integrators. Risk reduction depends on workflows and governance as much as tooling.
These constraints are why a purely IT style approach to vulnerability scanning and pentesting often produces either limited coverage or unacceptable operational risk.
A practical framework for SCADA cyber security (architecture, detection, and validation)
Use the following framework to structure a SCADA cyber security program. It is designed to be actionable for OT security architects, control engineers, and red teams.
Step 1: Build an OT and SCADA asset inventory that is operationally meaningful
Go beyond “what devices exist” and capture:
- Role in the process (criticality, safety relevance)
- Communications dependencies (who talks to whom, over which protocols)
- Management plane dependencies (engineering tools, backup/restore paths)
- Remote access paths (vendors, integrators, jump hosts)
This inventory is what makes later steps defensible and auditable.
Step 2: Implement SCADA network segmentation based on zones and conduits
Segmentation should reflect trust boundaries and process dependencies:
- Separate enterprise IT from OT with a clear industrial DMZ
- Segment supervisory systems from controllers where feasible
- Isolate engineering workstations and restrict programming access paths
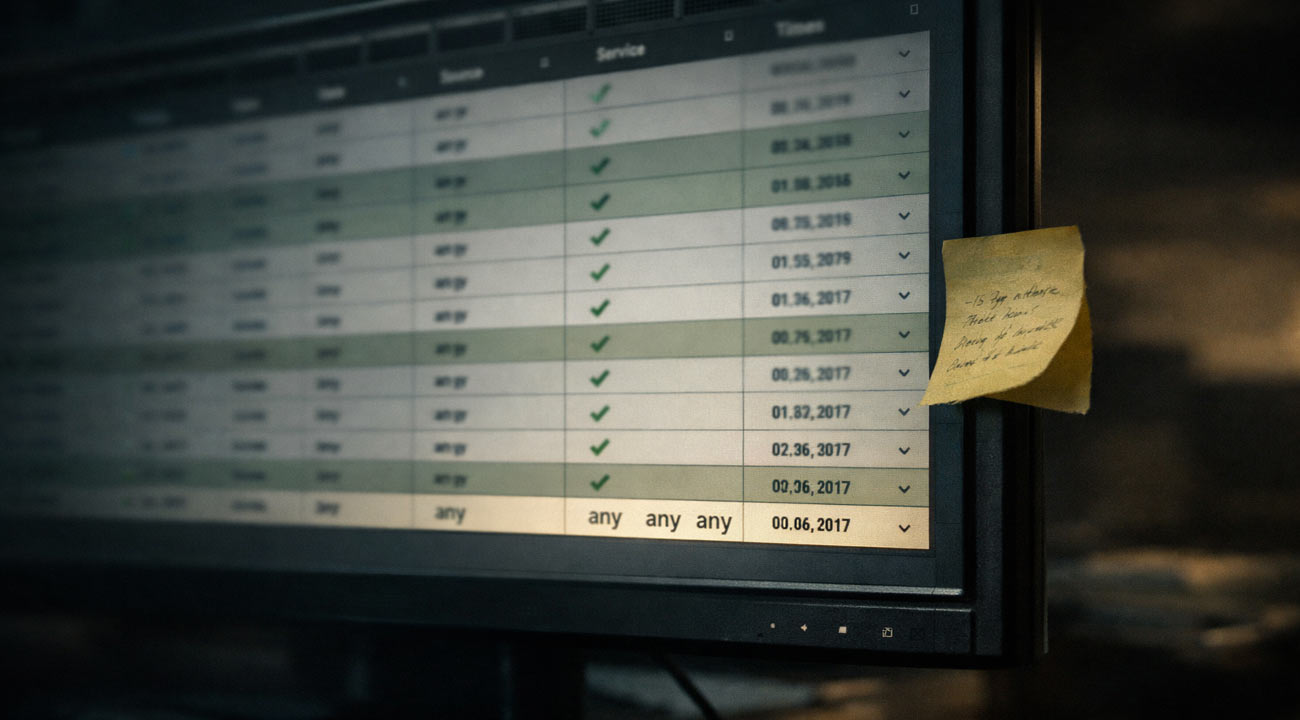
- Tighten east west communication using allowlists, not broad “any any” rules
In many environments, segmentation improvements are the fastest way to reduce blast radius, but only if they are validated against real traffic and operational needs.
Step 3: Harden identity, access, and remote operations
Common high value moves include:
- Strong identity and MFA for remote access, with short lived access grants
- Remove persistent vendor VPNs where possible, and gate access through monitored jump hosts
- Restrict who can reach programming ports and engineering services
- Separate operator accounts from engineering level privileges
Step 4: Deploy SCADA security monitoring that understands industrial behavior
SCADA security monitoring works best when it combines:
- Passive network visibility for industrial protocols
- Baselines for normal command patterns and controller communications
- Alerts mapped to operational impact (for example, logic download events, firmware changes, unexpected write commands)
- Clear incident playbooks that include operations and engineering
If you are building an overall program roadmap, Frenos also maintains a broader view in the Complete Guide to OT Security: Protecting Industrial Control Systems.
Step 5: Run SCADA vulnerability assessment and SCADA penetration testing, safely
This is where many programs stall. Traditional approaches can be limited by:
- Fragility concerns that reduce test depth
- Change freezes that delay remediation validation
- Inability to test “what if” scenarios like ransomware in a historian tier or lateral movement from remote access to engineering
A safer approach is to validate controls in a digital twin of the OT environment, where you can simulate real attack paths without introducing risk to production. Frenos focuses on full-scope testing through simulation, including attack path mapping to high risk assets and near-zero assessment downtime where feasible, depending on the data available and the environment constraints. For a concrete description of the testing model, see Platform 3.0 Simulated OT Penetration Testing for Industrial Environments.
Step 6: Close the loop with continuous security validation
Controls drift. Firewall rules change. Vendors add remote access exceptions. Engineering images get cloned. The goal is not a one time report, it is repeatable validation:
- Re-run high value scenarios after major changes
- Track remediation to verified outcomes, not just tickets closed
- Use attack path results to prioritize the smallest set of fixes that break the most risk chains
For teams exploring automation, agentic workflows can help coordinate analysis and retesting across complex environments, but they still need high fidelity context. If relevant, review OT Agentic AI to see how this is evolving in OT security programs.
Digital twin based testing: how to validate SCADA defenses without disrupting production
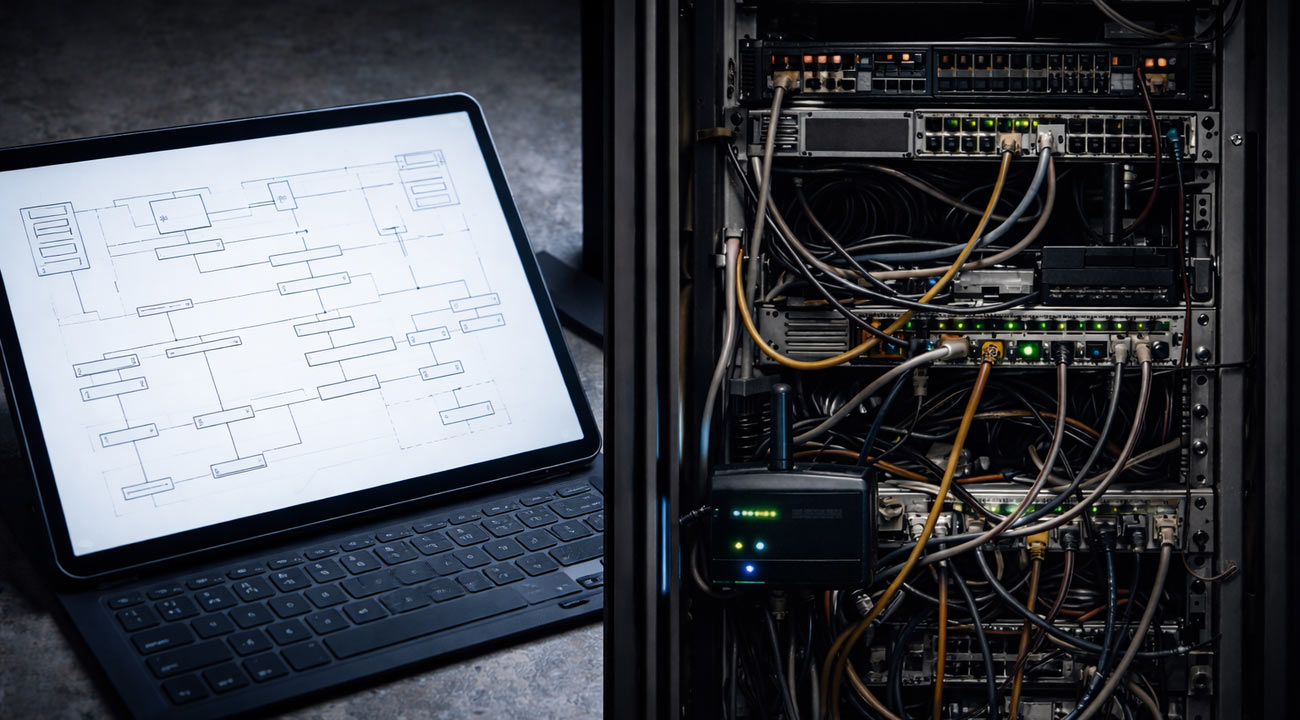
A digital twin for OT security testing is a modeled representation of the industrial environment that captures the assets, configurations, and communications patterns needed to simulate realistic attacker behavior and control system responses.
What you can validate in a twin that is hard to validate in production:
- End to end attack paths (for example, remote access to jump host to engineering workstation to controller write capability)
- The real security impact of segmentation rules, including unintended dependencies
- The effect of credential compromise and privilege escalation in the engineering plane
- Detection logic quality for SCADA intrusion detection and monitoring rules
- Recovery workflows in ransomware like scenarios without risking downtime
What data sets are typically needed
Most organizations are “mature enough” if they can provide some combination of:
- Network topology and IP plans
- Firewall and routing configurations
- Asset lists and software versions (even partial)
- Remote access architecture and user groups
- Representative traffic captures or protocol baselines, if available
You do not need perfect data on day one. The twin can be improved iteratively, as long as stakeholders agree on scope and validation objectives.
How outcomes should be delivered to be useful
To drive remediation, results should map technical findings to operational risk:
- Attack paths tied to specific assets and trust boundaries
- Reproducible steps, including preconditions
- Prioritized fixes that break multiple paths (for example, changing one conduit rule set, hardening one remote access tier, restricting one engineering function)
- Retest evidence showing that fixes actually reduced exposure
This approach is not a replacement for all on system validation, but it is a way to get deeper, faster coverage safely, and to make continuous validation feasible.
What to expect from a SCADA cyber security assessment (deliverables and timeline considerations)
A credible assessment should answer four questions: what can go wrong, how could it happen, how likely is it given your architecture and operations, and what should you do first.
Typical deliverables (adapt to your environment)
- Asset and communication dependency mapping that explains real trust relationships
- SCADA vulnerability assessment results with OT context (what is exploitable, what is not, and why)
- Attack path analysis showing how adversaries could reach high consequence functions
- Control recommendations focused on segmentation, remote access, identity, and monitoring
- Validation plan for retesting after remediation
Timeline depends on scope and data availability
Duration varies based on environment size, data quality, and stakeholder access. Digital twin based approaches can reduce the need for production touchpoints and reduce downtime, but they still require coordination to collect configurations and validate assumptions with engineering and operations.
A practical way to start is to pick a high value slice such as one plant, one remote site set, or one critical process line, then expand coverage once the model and methodology are proven.
FAQs
Will SCADA security testing disrupt production?
It can, if testing relies on active scanning, intrusive exploitation, or uncontrolled traffic in the live control network. A safer model is to validate scenarios in a digital twin, then perform only the minimal on system checks required for confirmation. This reduces operational risk while still producing actionable attack path and control validation outcomes.
Is digital twin based testing better than a traditional SCADA penetration test?
It is better for breadth and repeatability when production constraints limit what you can test. Traditional pentesting can still be valuable for targeted validation on specific assets or for confirming exploitability under real conditions. Many teams use a hybrid approach: simulate full scope scenarios safely, then selectively validate high risk findings on systems with strict change control.
How long does a SCADA vulnerability assessment or SCADA penetration testing effort take?
It depends on scope, site count, and how quickly data can be collected. Programs often move faster when they start with a clearly bounded environment and a defined set of scenarios (remote access abuse, engineering workstation compromise, segmentation bypass). Digital twin based methods can reduce scheduling friction because they minimize production touchpoints.
What do we get at the end of an OT and SCADA security assessment?
You should expect more than a list of CVEs. Useful outputs include mapped attack paths to high consequence assets, prioritized remediation actions that break those paths, and evidence based retesting guidance. Where applicable, results should also inform monitoring rules and incident response playbooks that align with operations.
Do we need perfect data sets to build a digital twin for SCADA security validation?
No. You need enough information to model key trust boundaries, access paths, and communications dependencies. Many organizations start with partial inventories, firewall exports, and remote access documentation, then improve fidelity iteratively as findings reveal what additional data will increase accuracy.
Call to Action
SCADA systems are hard to secure because they were engineered for continuous control, not for frequent change or aggressive testing. The fastest path to measurable risk reduction is to combine sound architecture (segmentation and access control), OT aware monitoring, and validation that proves the controls work in realistic attack scenarios. If you want full-scope testing without risking production disruption, request an OT Security Assessment with Frenos.


.jpg)
