SCADA environments sit at the intersection of legacy engineering constraints, always-on operations, and high-consequence outcomes. That combination makes them attractive to adversaries and difficult for defenders. Unlike traditional IT, you cannot simply patch aggressively, scan continuously, or run exploit-heavy tests against production without risking downtime, safety incidents, or process instability.
This article explains what “SCADA cyber security” means in practical terms, why attackers prioritize SCADA and broader OT environments, and how critical infrastructure teams can validate controls through SCADA vulnerability assessment and SCADA penetration testing approaches that do not touch production systems. Where relevant, we reference digital twin based validation as described in How Digital Twins Enable Safe, Comprehensive OT Security Testing and Digital Twins in OT Cybersecurity, plus how simulated testing can be operationalized in Platform 3.0 Simulated OT Penetration Testing.
What SCADA cyber security covers (concise definition)
SCADA cyber security is the set of technical and operational controls that protect supervisory control and data acquisition systems and their connected field assets, including:
-
Control system endpoints: HMIs, engineering workstations, historians, OPC servers, domain services where present, jump hosts, and vendor support paths.
-
Communications and protocols: Industrial Ethernet, serial gateways, and protocols such as Modbus, DNP3, IEC 60870-5-104, OPC Classic, and OPC UA. The security challenge is not only confidentiality but integrity and availability of control signals and telemetry.
-
Architecture and trust boundaries: Segmentation between enterprise IT and OT, cell and area zoning, remote access design, and the security of cross-boundary services such as patch distribution, identity, time services, and data replication.
-
Detection and response: SCADA security monitoring, intrusion detection tuned to industrial protocols, and incident response that accounts for operational safety and process constraints.
A useful way to frame SCADA cyber security is: prevent unsafe control, detect abnormal control, and recover operations without causing secondary impact.
Why SCADA systems are prime targets for cyber attacks
SCADA is targeted because it combines high impact, asymmetric access paths, and historically fragile change management.
High-consequence outcomes
An attacker does not need to “own the enterprise.” If they can influence setpoints, disable alarms, or disrupt view of the process, they can create financial loss, environmental impact, safety risk, and regulatory exposure. This is especially true in energy, water, pharmaceuticals, oil and gas, manufacturing, and transportation.
Long asset lifecycles and constrained patching
Many SCADA components stay in service for a decade or more. Patch cycles are tied to production windows and vendor qualification. That leaves known vulnerabilities unremediated longer than typical IT risk models assume.
Flat networks and inherited trust
Many sites still have broad Layer 2 reachability in OT, permissive firewall rules between zones, or shared services that create transitive trust. Once an attacker lands in one part of OT, lateral movement can be simpler than in mature IT environments.
Remote access and third-party dependency
Supportability drives connectivity: vendor VPNs, remote engineering, historian replication, and contractor access. These paths are operationally necessary, but they are also common initial access vectors.
Limited visibility at the protocol and process layer
Security teams often lack deep SCADA telemetry or context around “what good looks like” for a given process. Without that, it is hard to distinguish engineering activity from malicious manipulation.
The net effect: adversaries often view SCADA as an environment where a small foothold can lead to outsized results, especially when defenders cannot safely test assumptions in production.
Common attack paths in SCADA environments (what to look for)
For OT security architects and red teams, it helps to think in repeatable attack paths rather than isolated vulnerabilities. Common patterns include:
-
IT-to-OT pivot through shared services
Examples: mis-scoped firewall rules, shared Active Directory, poorly isolated patch servers, or data diodes that were bypassed for operational convenience. Risk: enterprise compromise becomes a pathway to engineering assets.
-
Compromise of engineering workstations and toolchains
Engineering workstations often have broad privileges and protocol reach. If an attacker controls the workstation used to configure PLCs or RTUs, they can change logic or parameters with legitimate tooling.
-
Remote access abuse
Examples: stolen VPN credentials, misconfigured remote desktop gateways, vendor remote support tools, and unmanaged jump hosts. Risk: authenticated access can look “normal” unless you correlate actions with change windows and process context.
-
Weak segmentation inside OT
Even where a perimeter exists, internal OT segmentation may be minimal. If the HMI subnet can reach every controller, an attacker has many options once inside.
-
Protocol-level manipulation and replay
Some industrial protocols lack authentication or integrity by default. Attackers may write coils/registers, spoof responses, or replay valid traffic to mask changes.
These paths are why SCADA security monitoring and SCADA intrusion detection should focus not only on malware indicators, but also on control actions, engineering functions, and unusual communication patterns between zones.
A practical framework for SCADA cyber security: assess, harden, monitor, validate
A workable program for SCADA cyber security can be structured into four repeating phases. The key is to treat validation as continuous, not a one-time exercise.
-
Assess: build an evidence-based risk picture
Scope what matters: critical process areas, safety-related systems, and highest-impact control loops. Inventory should include assets, firmware versions where available, installed software on HMIs/engineering workstations, and OT network paths. For a SCADA vulnerability assessment, prioritize:
- Externally reachable or cross-zone reachable services
- Remote access infrastructure
- Engineering stations and configuration repositories
- Protocol gateways (OPC, terminal servers, serial-to-IP)
-
Harden: reduce reachable attack surface
Typical high-value hardening actions:
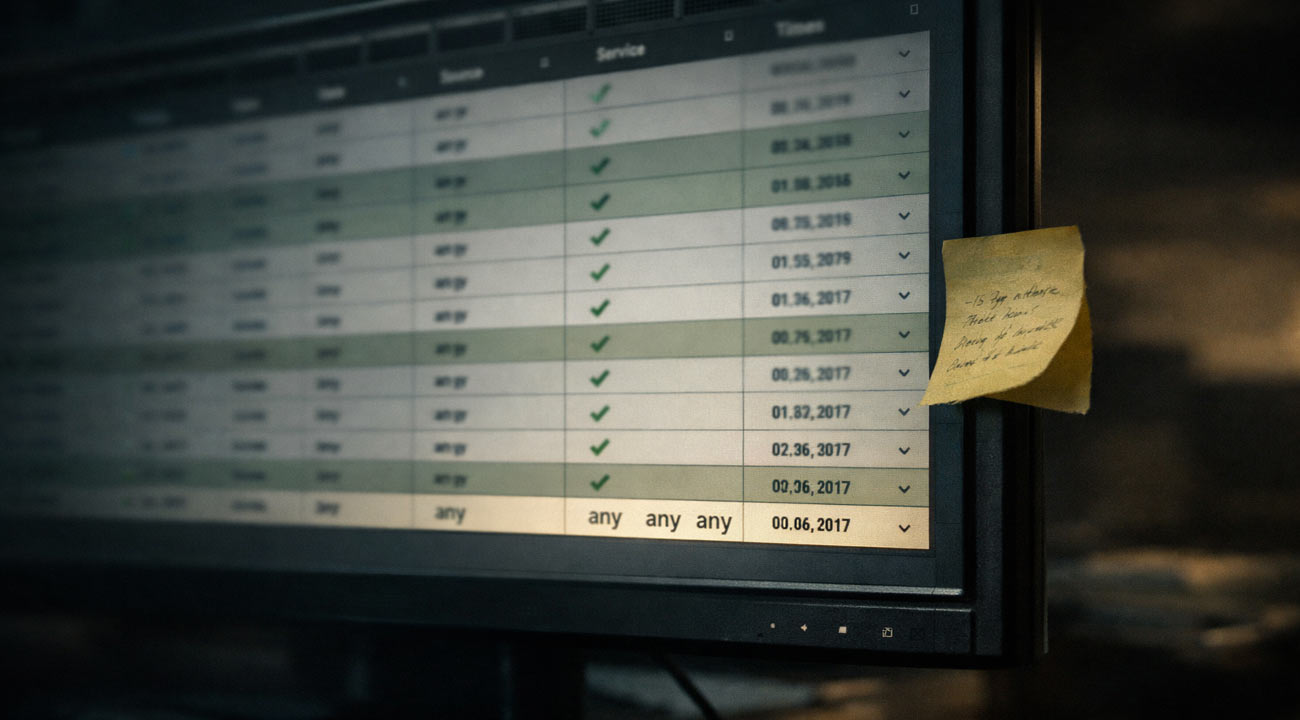
- Implement SCADA network segmentation using zones and conduits aligned to operations, not org charts
- Enforce least privilege for engineering functions and remove shared accounts
- Constrain remote access with jump hosts, MFA, session recording, and time-bound access
- Reduce “any-any” rules and document required flows between cells
-
Monitor: detect abnormal behavior with context
Effective SCADA security monitoring combines:
- Network-based visibility into industrial protocols
- Alerts tuned to engineering operations (downloads, firmware writes, configuration changes)
- Baselines per cell or process area to reduce noise
- Clear handoffs to operations for triage and safety checks
-
Validate: prove controls work under realistic attack
This is where many programs struggle. Traditional SCADA penetration testing can be high risk in production because packet floods, aggressive scanning, or exploit attempts can crash fragile systems or trigger safety instrumented responses. Yet without realistic validation, segmentation and monitoring remain assumptions.
Digital twin based validation addresses that gap by allowing full-scope OT and SCADA security testing without touching production systems. Instead of debating whether a control “should” work, you can simulate the attack path end-to-end in a representative environment and measure what an attacker could reach, change, and persist on. For more on this approach, see Digital Twins in OT Cybersecurity.
SCADA vulnerability assessment vs SCADA penetration testing: what’s the difference?
Both are useful, but they answer different questions.
SCADA vulnerability assessment
Goal: identify exposures and weaknesses such as outdated software, insecure services, misconfigurations, weak authentication, and risky network paths. Deliverables typically include a prioritized list of findings and remediation guidance. Strength: broad coverage and repeatability. Limitation: it may not prove exploitability or real operational impact.
SCADA penetration testing
Goal: demonstrate how an adversary could chain weaknesses into an attack path, including privilege escalation and lateral movement to high-consequence assets. Strength: realistic adversary thinking and impact demonstration. Limitation: in production OT, the safest version of a pentest is often heavily constrained, which can limit realism.
A practical approach in critical infrastructure is to combine both: use assessment to map exposure, then validate the highest-risk attack paths through controlled exploitation and simulation, ideally in a way that avoids production disruption.
How to test SCADA security without disrupting production: digital twin based validation
The core operational objection to SCADA penetration testing is legitimate: “Will this disrupt production?” In many plants, the safest answer is to avoid intrusive testing on live controllers and fragile Windows-based engineering stacks.
A digital twin of the industrial environment changes the tradeoff. Instead of connecting tools to production networks, you replicate the relevant parts of the environment so you can:
-
Simulate adversary behavior safely
Run realistic sequences such as initial access, credential access, OT lateral movement, and attempts to reach specific controllers or HMIs, without risking a plant trip.
-
Validate segmentation and reachability
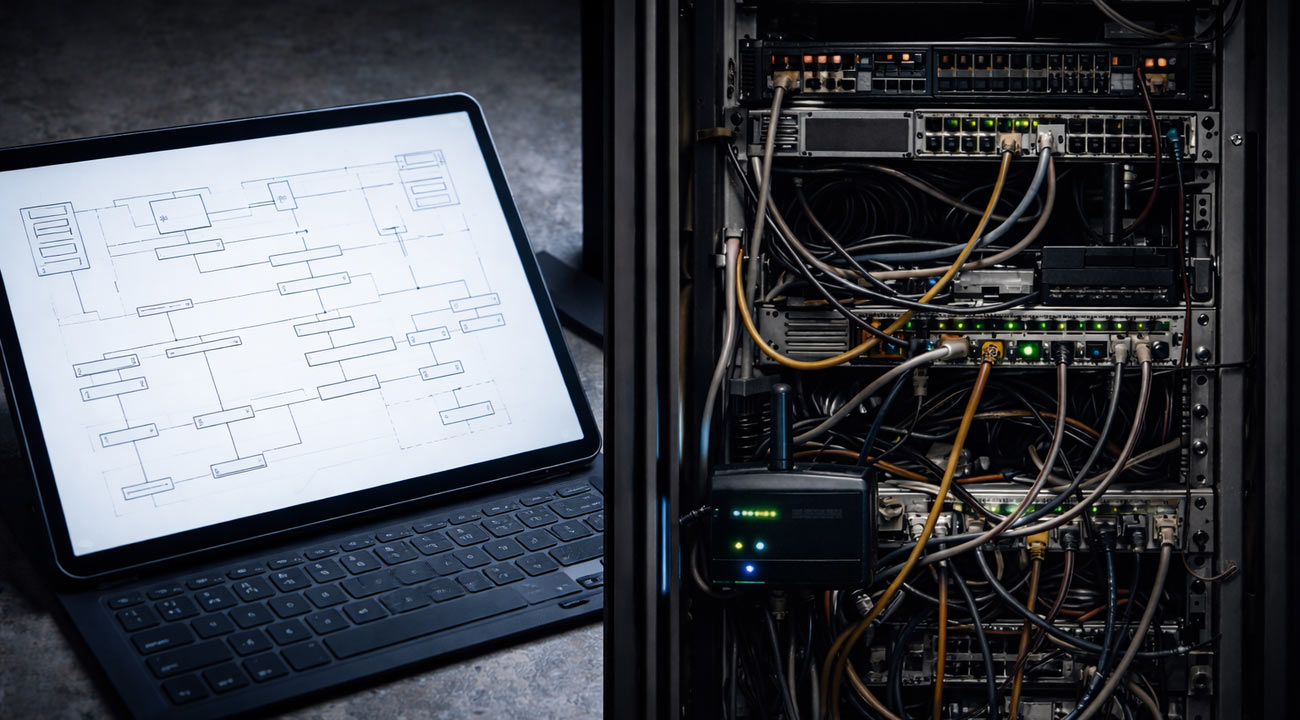
Test whether conduits truly restrict movement. For example: can an attacker from a contractor zone reach an engineering workstation VLAN? Can they pivot from historian services into control cells?
-
Measure detection coverage
Evaluate SCADA intrusion detection and SOC alerting on realistic traffic and attack sequences. You can check whether alerts trigger at the right points and whether the triage data is sufficient.
-
Produce defensible remediation priorities
Instead of a long list of CVEs, you can map attack paths to the highest-risk assets and show which control breaks the chain most effectively.
Frenos’ differentiator is enabling full-scope OT and SCADA security testing without touching production systems by using a digital twin to simulate real cyberattacks. This supports near-zero assessment downtime (where feasible, depending on environment and data availability) and repeatable validation cycles. A deeper look at simulated testing is covered in Platform 3.0 Simulated OT Penetration Testing.
If you are considering whether you are “mature enough” for a digital twin, maturity is less about perfection and more about data accessibility. Most organizations can start with a focused twin of the highest-criticality zones and expand over time. The method is described in more detail in How Digital Twins Enable Safe, Comprehensive.
What to expect from an OT and SCADA security assessment (timeline and outputs)
Two questions consistently come up: “How long does it take?” and “What do we get at the end?” The right answer depends on scope, access constraints, and data quality, but the outputs should be concrete.
Typical phases
-
Scoping and data intake
Confirm the operational boundaries, critical processes, and testing constraints. Gather diagrams, asset inventory exports if available, firewall rulesets, remote access architecture, and monitoring telemetry.
-
Architecture and exposure analysis
Review segmentation design, trust relationships, identity dependencies, and remote access. Identify likely attack paths and prioritize targets.
-
Controlled validation and simulation
Validate reachability, misconfigurations, and attack chains in a safe way. Where production testing is allowed, keep it non-intrusive and coordinated with operations. Where production testing is not acceptable, use a representative digital twin environment.
-
Reporting and remediation planning
You should expect:
- An attack path view that maps how an attacker could move to highest-risk assets
- A prioritized remediation backlog tied to risk reduction, not just severity scores
- Specific recommendations for SCADA network segmentation improvements
- Gaps and tuning guidance for SCADA security monitoring and intrusion detection
- Optional retest plan for continuous validation
If AI-enabled attackers are a concern, it is worth considering how automation affects both offense and defense, particularly around scale and repeatability.
Related perspective: AI Is Arming Both Sides of Cybersecurity But Only One Side Has a Plan to Scale.
FAQs
Will SCADA cyber security testing disrupt production?
It does not have to. Traditional intrusive testing on live OT can create risk, especially with fragile endpoints and safety constraints. A safer option is to validate attack paths in a digital twin of the industrial environment, enabling full-scope testing without touching production systems while still measuring reachability, exploit chains, and detection coverage.
Is a digital twin approach better than a traditional SCADA penetration test?
It is complementary. Traditional SCADA penetration testing can be valuable, but it is often constrained in production, which can reduce realism. Digital twin based validation allows realistic attacker simulation and repeatable testing cycles without operational disruption, making it well-suited for continuous security validation and for testing scenarios you would not risk on live systems.
How long does a SCADA vulnerability assessment or penetration test take?
Time varies by scope and data availability. Focused assessments can move faster when network diagrams, asset inventories, and access paths are well documented. Broad, multi-site environments and complex vendor access models take longer. A practical approach is to start with the highest-criticality zones, produce prioritized attack paths and remediation actions, then expand coverage iteratively.
What deliverables should we require at the end?
Require outputs that help you reduce risk quickly: documented attack paths to highest-risk assets, a prioritized remediation backlog tied to the control that breaks each path, segmentation and remote access findings, monitoring and intrusion detection gaps with tuning recommendations, and a retest plan to confirm fixes.
Do we need perfect data to create a digital twin for SCADA security testing?
No. You need enough fidelity to represent critical trust boundaries, key assets, and the communications that matter for attack paths. Many organizations start with partial data and build a targeted twin around crown-jewel areas such as engineering workstations, remote access, and critical control cells, improving coverage as inventories and diagrams mature.
Call to Action
SCADA environments are targeted because small access advantages can create high-consequence outcomes, and many defenses are hard to validate safely in production. If you want to move beyond assumptions and confirm real attack paths, request an OT Security Assessment to evaluate your SCADA exposure, segmentation, monitoring, and detection readiness using safe, non-disruptive testing methods.


.jpg)
