If you read my Day One post, you know we ended the day installed, integrated, and waiting. Our consequence-free digital twin was built in under twelve minutes. Frenos was ready. But SAIRA couldn't run attack path simulations yet because the SPAN ports for Claroty and Dragos hadn't been turned on. No asset inventory data, no full environmental context.
That changed at 7 PM on Day One.
SPAN Ports Go Live
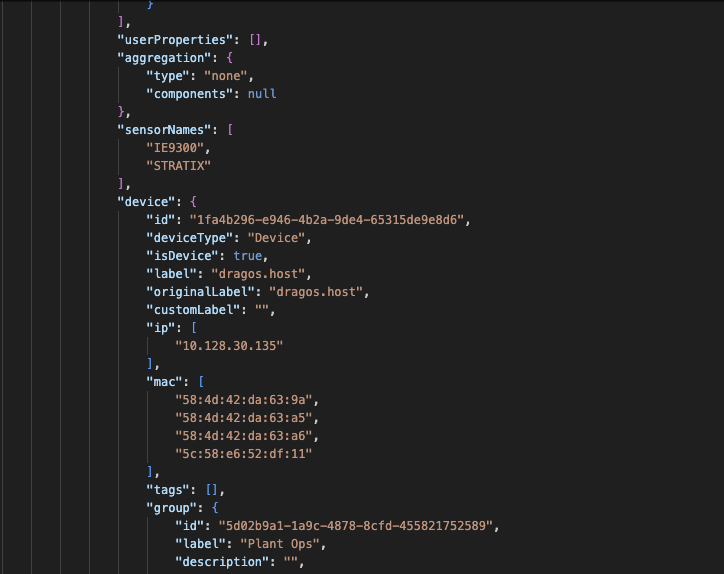
Booz Allen turned on the SPAN ports at 7 PM, and Claroty and Dragos immediately began deep packet inspection and asset discovery across the POC Pavilion's manufacturing environment. Their datasets started enriching in real time, giving Frenos exactly what we needed to complete the picture.
This is how the architecture is supposed to work. Visibility platforms do what they do best.
Frenos takes that data and turns it into offensive context. Complementary by design.

Day Two. New Configs, New Twin
Day Two started with a notification from Booz Allen Hamilton. Firewall and topology changes had been made overnight to support the POC Pavilion environment. New rules, new routing, new network architecture.
For a lot of platforms, that means going back to square one. Reconfiguring. Re-baselining. Waiting.
For us, it meant ingesting the updated configurations and rebuilding our digital twin to reflect the current state of the environment. Which took minutes.

154,000 Simulations. 17 Minutes and 7 Seconds.
With the updated digital twin live and the enriched asset data from Claroty and Dragos flowing in, we officially kicked off our attack path simulations.
We selected three assumed breach networks: the iDMZ, Plant Operations, and Enterprise. These represent realistic starting points for an adversary who has gained initial access and is looking to move laterally toward the most critical assets in the environment.
SAIRA went to work.
154,000 attack path simulations. 17 minutes and 7 seconds.

Out of those 154,000 simulations, SAIRA identified 18 validated attack paths from our assumed breach networks into the critical Rockwell and Siemens zone. Not theoretical. Not based on CVSS scores or scanner output. These are paths that SAIRA confirmed are exploitable given the actual controls, firewall rules, routing, and configurations modeled in the digital twin.

That's the difference between a vulnerability list and a security posture assessment. 154,000 possible paths narrowed down to the 18 that actually matter. That's where your team should be spending their time.
Visibility Coverage
Worth calling out: with the data flowing in from Claroty and Dragos, we're seeing 86% asset coverage across the POC Pavilion network, with 41% of the devices fully enriched. That's a testament to the quality of visibility data our partners are producing. The better the input, the sharper SAIRA's analysis becomes. Great partners make great results.
What This Means
On Day One we proved Frenos can be installed in under twelve minutes on a network we've never seen before. On Day Two we proved that once the environmental data is flowing, SAIRA can assess 154,000 attack paths in 17 minutes and surface the ones that represent real risk to your most critical assets.
More to come as the week continues. Stay tuned.
Frenos. Build your resilience.


.jpg)

.jpg)
